HIPAA compliance is non-negotiable for protecting patient data and avoiding hefty penalties. If your practice handles Protected Health Information (PHI), you must safeguard patient records, ensure privacy, and follow federal standards. This guide outlines the key steps to meet HIPAA requirements:
- Assign Privacy and Security Officers: Designate individuals to oversee privacy policies, enforce security measures, and manage compliance tasks.
- Develop Policies and Procedures: Create detailed documents tailored to your workflows, covering PHI usage, patient rights, and breach protocols.
- Conduct Risk Assessments: Regularly evaluate threats to electronic PHI (ePHI), identify vulnerabilities, and implement mitigation plans.
- Implement Technical Safeguards: Use encryption, access controls, and audit logs to secure patient data.
- Train Staff: Educate all team members on HIPAA rules, with role-specific training and documented sessions.
- Sign Business Associate Agreements (BAAs): Ensure vendors handling PHI comply with HIPAA through signed agreements.
- Maintain Records and Logs: Keep audit trails and compliance documentation for at least six years.
- Prepare for Breaches: Have a response plan to quickly contain, report, and address data breaches.
Key Stats:
- 546 healthcare breaches affected 42M individuals in the first nine months of 2025.
- HIPAA violations can cost up to $2M annually for willful neglect.
- Common issues include weak passwords, unencrypted devices, and missing risk assessments.

8-Step HIPAA Compliance Checklist for Healthcare Practices
Appoint a Privacy and Security Officer
Every HIPAA-covered entity is required to officially assign two critical roles: a Privacy Official and a Security Officer. The Privacy Official oversees privacy policies and ensures patient rights are protected, while the Security Officer focuses on implementing technical measures to safeguard electronic protected health information (ePHI). In smaller practices, like aesthetic clinics, these roles might be combined and handled by a practice manager or lead nurse.
The appointment must be documented in writing, complete with a detailed job description signed by executive leadership. This document should clearly outline the officer's authority to enforce policies, access records, and report directly to senior management. Additionally, the organization's Notice of Privacy Practices should include the contact person's name or title, so patients know where to direct complaints or concerns.
"If no one is clearly assigned to oversee privacy compliance, your practice is out of alignment with HIPAA requirements." - Complydome
When selecting someone for these roles, prioritize candidates who have a strong understanding of HIPAA, HITECH, and state-specific regulations. They should also be familiar with your electronic health records (EHR) and billing systems and possess strong communication skills to effectively train staff. Ensure they have dedicated time to manage compliance tasks, such as conducting quarterly risk assessments, overseeing vendors, and coordinating breach responses. For example, in 2021, a pediatric clinic faced a $10,000 penalty for failing to document a Privacy Official. This underscores the importance of choosing someone who is knowledgeable about both regulatory and operational requirements.
To maintain accountability, establish a regular reporting schedule - quarterly, for instance - so the officer can share compliance updates and metrics with your leadership team. This practice demonstrates your organization’s commitment to HIPAA compliance. Don’t forget to appoint a qualified backup to handle responsibilities during absences, and keep all designation letters and job descriptions on file for at least six years.
sbb-itb-02f5876
Create Privacy Policies and Procedures
After appointing your Privacy and Security Officers, the next step is to create detailed, written policies that outline how your practice manages patient health information. Since HIPAA doesn’t provide a universal template, your policies need to be tailored to your workflows, technology, and state-specific regulations. These policies are essential for defining strict rules on how protected health information (PHI) is used and disclosed - whether it’s for routine treatment notes, insurance billing, or even marketing communications.
Your policies should address several critical areas:
- Permitted uses and disclosures: Clearly define what’s allowed for Treatment, Payment, and Healthcare Operations (TPO), as well as disclosures required by law (e.g., public health reporting).
- Patient authorizations: Specify activities that require written consent, such as marketing, the sale of PHI, or handling psychotherapy notes.
- Minimum necessary standard: Set up role-based access controls to ensure employees only access the information necessary for their duties.
- Patient rights: Outline procedures for patients to access their records, request amendments, and receive an accounting of disclosures.
These principles serve as the groundwork for crafting the detailed policies and operational procedures discussed below.
Write Privacy Policies
Start by drafting a Notice of Privacy Practices (NPP). This document should explain how your practice uses PHI, outline patients’ rights, and provide instructions for filing complaints. Make sure every patient receives a copy at their first visit, and display it prominently in your office and on your website. Beyond the NPP, your policies should address:
- Authorization requirements
- Minimum necessary disclosures
- Timelines for patient access requests (usually within 30 days)
- Breach notification protocols
Include a sanctions policy that details progressive disciplinary actions for staff who violate privacy rules, along with a formal, non-retaliatory process for handling complaints. If your state’s privacy laws are stricter than HIPAA, ensure your policies meet those higher standards. Regular updates are crucial - review your policies at least once a year to account for changes in technology, workflows, or regulations.
Set Up Procedures
Policies establish the rules, but procedures translate them into actionable steps for day-to-day operations. Each policy should have a corresponding, step-by-step procedure with clearly defined tasks and responsibilities. For instance, if your policy requires identity verification before releasing records, your procedure should specify acceptable forms of ID, who verifies them, and how the process is documented.
Standardize workflows for common activities like PHI intake, information release, and handling patient access requests. Assign policy owners to ensure consistent enforcement. Use role-based access controls in your electronic systems to automatically uphold the minimum necessary standard. Provide templates for authorizations, Business Associate Agreements (BAAs), and breach notification letters to simplify compliance with legal requirements. Finally, organize all policies and procedures in a centralized repository, keeping them up to date and retaining documentation for at least six years.
| Policy Element | Operational Procedure (Implementation) |
|---|---|
| Minimum Necessary Standard | Role-based access controls; templated data sets for non-treatment workflows. |
| Patient Right of Access | Identity verification protocols; 30-day response timeline; cost-based fee schedules. |
| Breach Notification | Four-factor risk assessment tool; incident response playbooks; notification templates. |
| Workforce Oversight | Onboarding training; annual refreshers; graduated sanction policy for violations. |
| Business Associate Management | BAA inventory; pre-contract due diligence; periodic vendor monitoring. |
Perform Regular Risk Assessments
While HIPAA doesn't mandate a specific frequency for conducting a Security Risk Analysis (SRA), aiming for at least one assessment annually is widely regarded as a best practice. It's also smart to perform a fresh assessment after significant events like system upgrades, organizational shifts, or security breaches. The U.S. Department of Health and Human Services (HHS) emphasizes the importance of these assessments:
"An SRA is the foundation for achieving compliance with all other requirements of the HIPAA Security Rule."
The numbers don't lie: in the first nine months of 2025 alone, 546 healthcare breaches impacted 42 million individuals. Over the past five years, hacking-related breaches have skyrocketed by 256%, while ransomware-related incidents have surged by 264%. The Office for Civil Rights (OCR) has been vocal about the industry's shortcomings:
"The failure to implement basic HIPAA requirements, such as an accurate and thorough risk analysis and risk management plan, continues to be an unacceptable and disturbing trend within the health care industry."
A thorough risk assessment follows several key steps. Start by defining the scope of all systems handling electronic Protected Health Information (ePHI) and mapping how data flows through your organization. Then, identify potential threats and vulnerabilities, evaluate the likelihood and impact of each, and review your current safeguards. For smaller providers, the free Security Risk Assessment Tool from HHS can be a helpful guide. Automated platforms can speed up the process - reducing assessment cycles from 30–45 days to under 10 days - but remember, accuracy is more important than speed. This groundwork allows you to pinpoint vulnerabilities in the next phase.
Find Vulnerabilities
To uncover vulnerabilities, start by inventorying every location where ePHI is stored or accessed. This includes EHR systems, mobile devices, cloud storage, backup systems, USB drives, and even office equipment like copiers and fax machines. Trace how patient data moves through your practice - from intake forms and scheduling to billing and insurance - to spot any weak points.
Use a variety of methods to identify risks. Interview staff to understand their workflows, conduct physical walkthroughs to check workstation setups and access controls, review system configurations, and run technical scans to detect network vulnerabilities. Common issues include unpatched software, weak passwords, lack of encryption on portable devices, missing multi-factor authentication (MFA), and insufficient audit logging. It's also important to identify any "shadow IT", such as unauthorized apps or devices staff might be using.
To organize your findings, categorize threats into three main groups: cyberattacks (like phishing, ransomware, or hacking), human error (accidental disclosures, lost devices), and natural disasters (floods, fires, power outages). Document these risks using a risk matrix, which helps prioritize actions based on the likelihood and impact of each threat.
| Risk Level | Likelihood | Impact | Action Required |
|---|---|---|---|
| Critical | High | High | Urgent remediation; immediate action needed |
| High | Medium/High | High | Prioritized remediation; scheduled in 30–60 days |
| Medium | Medium | Medium | Remediation required; included in long-term roadmap |
| Low | Low | Low | Monitor; may not require immediate changes |
Create Risk Mitigation Plans
Once you've identified vulnerabilities, it's time to tackle them with a solid action plan. Start by prioritizing risks based on their severity, and focus first on "quick wins" - high-risk issues that can be resolved with minimal effort, such as enabling MFA for remote access or encrypting all laptops. Break your plan into 30-60-90 day milestones for critical issues and outline longer-term strategies for medium-level risks.
For each risk, decide on one of four treatments: mitigate, transfer, avoid, or accept. Effective plans often combine administrative measures (like updated policies, staff training, and Business Associate Agreements), physical safeguards (such as secure device disposal and controlled facility access), and technical defenses (like encryption, MFA, and audit logging).
To ensure accountability, use a RACI chart to assign clear roles: define who is Responsible for each task, who is Accountable for outcomes, who should be Consulted for input, and who needs to be Informed of progress. Set concrete deadlines and document every decision, including why certain risks are being accepted. Keep in mind that all risk assessment records must be retained for at least six years from their creation or last effective date.
Finally, make this a living process. Regularly test the effectiveness of your safeguards and conduct trigger-based assessments whenever major changes occur - like deploying new software, relocating offices, or onboarding new vendors. This isn't just about checking a compliance box; it's about actively protecting patient data and staying ahead of evolving threats.
Protect Electronic PHI (ePHI)
Once you've identified risks, the next step is putting technical safeguards in place to protect ePHI. HIPAA's Security Rule highlights five key standards: access control, audit controls, integrity, authentication, and transmission security. These are essential for shielding patient data from breaches and unauthorized access.
Consider this: In 2021, a hospital in Texas paid $3 million after failing to review audit logs for over six months, allowing unauthorized access to ePHI to go unnoticed. Similarly, BayCare Health System settled for $800,000 in 2025 due to inadequate system monitoring, while Syracuse ASC paid $250,000 the same year for unencrypted devices and weak access controls.
It's important to note that "addressable" specifications under HIPAA aren't optional. You need to evaluate whether they are suitable for your practice. If a specification isn't feasible, document your reasoning and implement an alternative solution. With risks identified, the focus now shifts to applying technical safeguards that directly secure ePHI.
Set Up Role-Based Access
Role-based access control (RBAC) ensures staff members can only access the patient data they need for their specific roles. For example, front desk staff may need access to scheduling and demographic information, but they shouldn't be able to view clinical notes or lab results unless their role requires it.
Start by assigning unique user IDs for every team member - shared accounts are not allowed under HIPAA. Use strong passwords and enforce multi-factor authentication (MFA) for remote or privileged access. MFA is critical for protecting sensitive systems. Additionally, configure automatic logoffs or session locks after 5–15 minutes of inactivity to prevent unauthorized access to unattended workstations.
Establish formal clearance and termination procedures. Grant access only after proper authorization and revoke it immediately when roles change or employees leave. Automating deprovisioning can help ensure accounts are disabled promptly. Also, create emergency access procedures for situations where urgent access to critical ePHI is required.
| Safeguard Standard | Implementation Specification | Status |
|---|---|---|
| Access Control | Unique User Identification | Required |
| Emergency Access Procedure | Required | |
| Automatic Logoff | Addressable | |
| Encryption and Decryption | Addressable | |
| Audit Controls | Implement mechanisms to record/examine activity | Required |
| Integrity | Mechanism to authenticate ePHI (e.g., hashing) | Addressable |
| Authentication | Verify person/entity identity | Required |
| Transmission Security | Integrity Controls | Addressable |
| Encryption | Addressable |
Enable audit logs to track who accessed which records and when. Use a centralized Security Information and Event Management (SIEM) system to manage these logs, and review them at least weekly for unusual activity. This not only ensures compliance but also helps detect suspicious behavior early.
To strengthen these measures further, focus on encryption and firewalls.
Apply Encryption and Firewalls
Encryption is a critical defense against data breaches. For data at rest - stored on servers, laptops, or portable devices - implement AES-256 encryption, the standard recommended by NIST. This can include full-disk, database, and file-level encryption. For data in transit - such as information sent over networks, email, or web portals - enforce TLS 1.2 or higher (preferably TLS 1.3) and disable outdated protocols and ciphers.
Firewalls provide another layer of security by segmenting systems that handle ePHI from the rest of your network and restricting unnecessary traffic. Configure firewalls to allow only essential connections while blocking all others. Use them to create secure zones for platforms managing sensitive data.
To maintain data integrity, use methods like SHA-256 hashing, checksums, or digital signatures to detect any unauthorized changes to patient records. Retain all compliance documentation, including encryption policies, firewall configurations, and risk assessments, for at least six years from the date they were created or last updated. This demonstrates that you've taken reasonable steps to safeguard patient information effectively.
Allow Patient Access to Records
Once technical safeguards are in place, it's essential to ensure patients can easily and securely access their own health records.
Under HIPAA, patients have the right to access their Protected Health Information (PHI), which includes medical records, billing details, lab results, and other care-related data.
You must respond to access requests within 30 days, though a single 30-day extension is allowed if accompanied by a written explanation and a firm deadline. While you can require written requests and identity verification, the process must remain reasonable. For instance, avoid requiring an in-person visit if remote verification via phone or email is sufficient.
Patients should be able to receive their records in any accessible format - such as a secure PDF, portal download, paper copy, or USB drive. They can also authorize you to send their electronic PHI directly to a third party (like a family member or another provider) through a signed written directive. Fees must be limited to cost-based charges covering labor, supplies, and postage. You cannot charge for tasks like searching, retrieving, identity verification, or system maintenance. For electronic copies, a flat fee of no more than $6.50 is permitted.
In some cases, access may be denied. This includes situations involving psychotherapy notes kept separately, information prepared for legal proceedings, or when a licensed professional determines that access could endanger the safety of the patient or others. If you deny access, you must provide a timely written notice explaining the legal reason and, if applicable, inform the patient of their right to have the decision reviewed. When only part of a record is restricted, redact the denied sections and provide the rest. Always comply with state laws if they require faster response times or lower fees than HIPAA standards.
"Providing individuals with easy access to their health information empowers them to be more in control of decisions regarding their health and well-being." - HHS
Train Staff on HIPAA Rules
Training your staff on HIPAA rules is a critical part of safeguarding patient data and maintaining compliance. This applies to everyone - employees, volunteers, interns, and contractors. Federal regulations require it, and failing to document training can lead to serious penalties.
New hires should complete HIPAA training within 7–30 days before they gain access to patient records. After that, annual refresher sessions are necessary to keep HIPAA principles top of mind. If there are updates to privacy policies, new technology is introduced, or a security incident occurs, retraining should happen right away.
Training should be role-specific to ensure relevance and effectiveness:
- Front desk staff: Focus on discreet check-ins and secure communication practices.
- Clinical staff: Emphasize handling patient records and maintaining telehealth privacy.
- IT personnel: Cover encryption methods and audit log monitoring.
- Billing team: Train on proper release-of-information workflows.
Every training session must be documented. Keep records of names, dates, topics covered, and signed acknowledgments for at least six years. Without these records, regulators may assume the training never happened. For example, a physical therapy clinic had to pay a $35,000 settlement because it couldn’t provide documentation proving staff had been trained.
The consequences of inadequate training can be severe. PIH Health faced a $600,000 settlement after a phishing attack compromised 189,763 patient records. On top of organizational penalties, individual employees can face criminal charges, with fines up to $250,000 and prison sentences of up to 10 years for knowingly misusing Protected Health Information (PHI).
Effective training is a cornerstone of your clinic's HIPAA compliance efforts and strengthens the broader risk management framework you’ve established.
Sign Business Associate Agreements (BAAs)
After ensuring internal compliance, managing external vendors becomes essential for meeting HIPAA requirements. Any third-party vendor that handles patient records must sign a Business Associate Agreement (BAA) before accessing Protected Health Information (PHI). Without a signed BAA, both parties are in violation of HIPAA rules. This applies to a wide range of vendors, including EHR providers, billing services, cloud storage companies, transcription firms, IT support teams, and even document shredding services. BAAs are a cornerstone of a robust HIPAA risk management strategy.
"A BAA must be in place before the business associate creates, receives, maintains, or transmits PHI on behalf of the covered entity. Operating without a BAA is a HIPAA violation for both parties." - Anitha Rajmohan, Director - Cyber Assurance, Glocert
Take the case of Presence Health (now part of AMITA Health), which, in January 2017, paid a $475,000 settlement to the Office for Civil Rights (OCR). The investigation revealed the organization had failed to secure compliant BAAs with several vendors and omitted required provisions on breach notification and safeguards. According to OCR data, penalties for missing or incomplete BAAs can range from $100 to $50,000 per violation.
Each BAA must include specific provisions, such as:
- Permitted and prohibited uses of PHI
- Safeguards to protect PHI
- Detailed breach reporting timelines (e.g., exact days instead of vague terms like "promptly")
- Obligations for subcontractors
- Support for patient rights
- Access for HHS audits
- Terms for contract termination and data return or destruction
To stay organized, maintain a centralized, searchable repository for all signed BAAs. Set up automated alerts for expiration reminders at 90, 60, and 30 days. Additionally, request a list of subcontractors from vendors to ensure downstream BAAs are also in place.
Regularly review and update BAAs - at least annually or whenever there are regulatory or operational changes. A 2025 report revealed that only 11% of covered entities audited by the OCR had no compliance issues related to vendor oversight. Keeping BAAs up-to-date not only supports HIPAA compliance but also strengthens overall patient data security efforts.
Keep Audit Logs and Retain Records
Keeping detailed records of every interaction with patient data is a crucial step in meeting HIPAA compliance and strengthening your practice's risk management. According to HIPAA's Security Rule (45 C.F.R. §164.312(b)), covered entities must have mechanisms in place to document and review activities within systems that store electronic Protected Health Information (ePHI). This creates a digital trail that shows who accessed specific information, when it happened, and what actions were taken.
Track Record Access
Every audit log entry should capture six essential details: the user ID of the person accessing the data, an exact timestamp of the action, the specific action performed (e.g., viewed, edited, deleted), the patient record or file involved, the access location (like an IP address or device ID), and the outcome (success or failure).
"HIPAA audit logs serve as your organization's electronic paper trail, documenting every interaction with protected health information (PHI) to ensure accountability and regulatory compliance." - Robert Dougherty
Maintain three types of logs for comprehensive tracking:
- Application logs: Record user activity within software like EHR systems.
- System-level logs: Capture events such as logins and firewall activity.
- User logs: Track specific commands and access to PHI.
To prevent tampering, secure these logs with safeguards like encryption (AES-256), hashing, or write-once-read-many (WORM) storage. For paper records, use physical sign-out sheets to log access details.
Automating log collection with a centralized Security Information and Event Management (SIEM) system helps ensure a complete and accurate audit trail. Establish a Standard Operating Procedure (SOP) for reviewing logs regularly - weekly or monthly - to detect anomalies, such as emergency "break-glass" access or unusual activity during off-hours. Restrict access to audit logs to authorized personnel, like a Security Officer, to prevent unauthorized modifications.
Follow Retention Requirements
In addition to maintaining detailed logs, adhering to record retention requirements is a key element of HIPAA compliance. HIPAA mandates that compliance documentation, including audit logs, must be retained for at least six years from the date of creation or the last effective date, whichever is later. However, retention requirements for medical records vary based on state laws and CMS regulations. For instance:
- Medicare Advantage and Part D sponsors must retain records for 10 years.
- Many states require adult medical records to be kept for 7–10 years.
- Records for minors are often retained until the patient reaches the age of majority, plus an additional 2–10 years.
| Record Type | Retention Period | Governing Authority |
|---|---|---|
| HIPAA Compliance Docs (Policies, BAAs, Training) | 6 years | HIPAA |
| Audit Logs for PHI Access | 6 years (Recommended) | HIPAA / Best Practice |
| Adult Medical Records | 7–10 years (Varies by state) | State Law |
| Minor Medical Records | Age of majority + 2–10 years | State Law |
| Medicare Advantage Records | 10 years | CMS |
Always follow the longest applicable retention period based on HIPAA, state laws, CMS, or payer contracts. Create a written retention schedule that outlines each document type, its retention period, and the trigger event (e.g., last patient encounter or contract termination). Keep logs in their raw format for at least 6–12 months before compressing them. If litigation or an audit is expected, immediately halt the destruction of any relevant records. Once retention periods expire, securely dispose of PHI - use cross-cut shredding for paper records or NIST-standard media sanitization for electronic data - and ensure vendors provide a certificate of destruction.
Prepare a Breach Response Plan
Even with strong safeguards in place, data breaches can still happen. Healthcare continues to be the most expensive industry for data breaches, holding this position for 14 years straight as of 2025, with the average breach costing $7.42 million. For instance, in February 2024, Change Healthcare suffered a breach that impacted 192.7 million individuals, costing an estimated $2.87 billion. Having a clearly written breach response plan is critical to act quickly, meet federal deadlines, and reduce harm to patients.
A solid breach response plan builds on technical safeguards and audit practices. Start by assigning your HIPAA Privacy Officer to lead a response team, which should include the Security Officer, IT staff, and legal counsel. Train all staff to report potential breaches immediately to the Privacy Officer. When a breach occurs, the first step is containment. This means actions like recalling erroneous emails, disabling compromised accounts, and disconnecting affected systems from networks. At the same time, preserve all evidence by capturing audit logs, screenshots, and system images, while maintaining a strict chain of custody. Quick containment limits risks and lays the groundwork for effective follow-up.
The next step is performing a four-factor risk analysis to decide if the breach must be reported. This involves assessing the type of PHI involved, who accessed or received it, whether the data was actually viewed or acquired, and how much the risk has been mitigated. If the breach is reportable, notify affected individuals within 60 days of its discovery through first-class mail or email (if they’ve consented). For breaches involving 500 or more individuals, you must also notify the HHS Secretary and media outlets within the same 60-day window. For smaller breaches (fewer than 500 individuals), keep a log and report it to HHS within 60 days of the year’s end.
| Notification Type | Threshold | Deadline |
|---|---|---|
| Individual Notice | Any breach of unsecured PHI | Within 60 days of discovery |
| HHS Secretary Notice | 500+ individuals affected | Within 60 days of discovery |
| HHS Secretary Notice | < 500 individuals affected | Within 60 days of year-end |
| Media Notice | 500+ residents in a state | Within 60 days of discovery |
After notifications are sent, focus on preventing future incidents. Conduct a root-cause analysis to identify what went wrong and update your security policies as needed. Provide targeted training to staff to avoid similar issues, and document every step of the breach response in a log that must be kept for at least six years. Missing deadlines can lead to costly penalties - Presense Health, for example, paid a $475,000 settlement in 2017 after taking three months to notify the HHS Secretary and affected individuals, well beyond the 60-day requirement. Timeliness is critical, and delays can have serious consequences even if you eventually comply.
Use HIPAA-Compliant Software
Strengthen your technical safeguards by bringing all your systems together under a single, HIPAA-compliant platform.
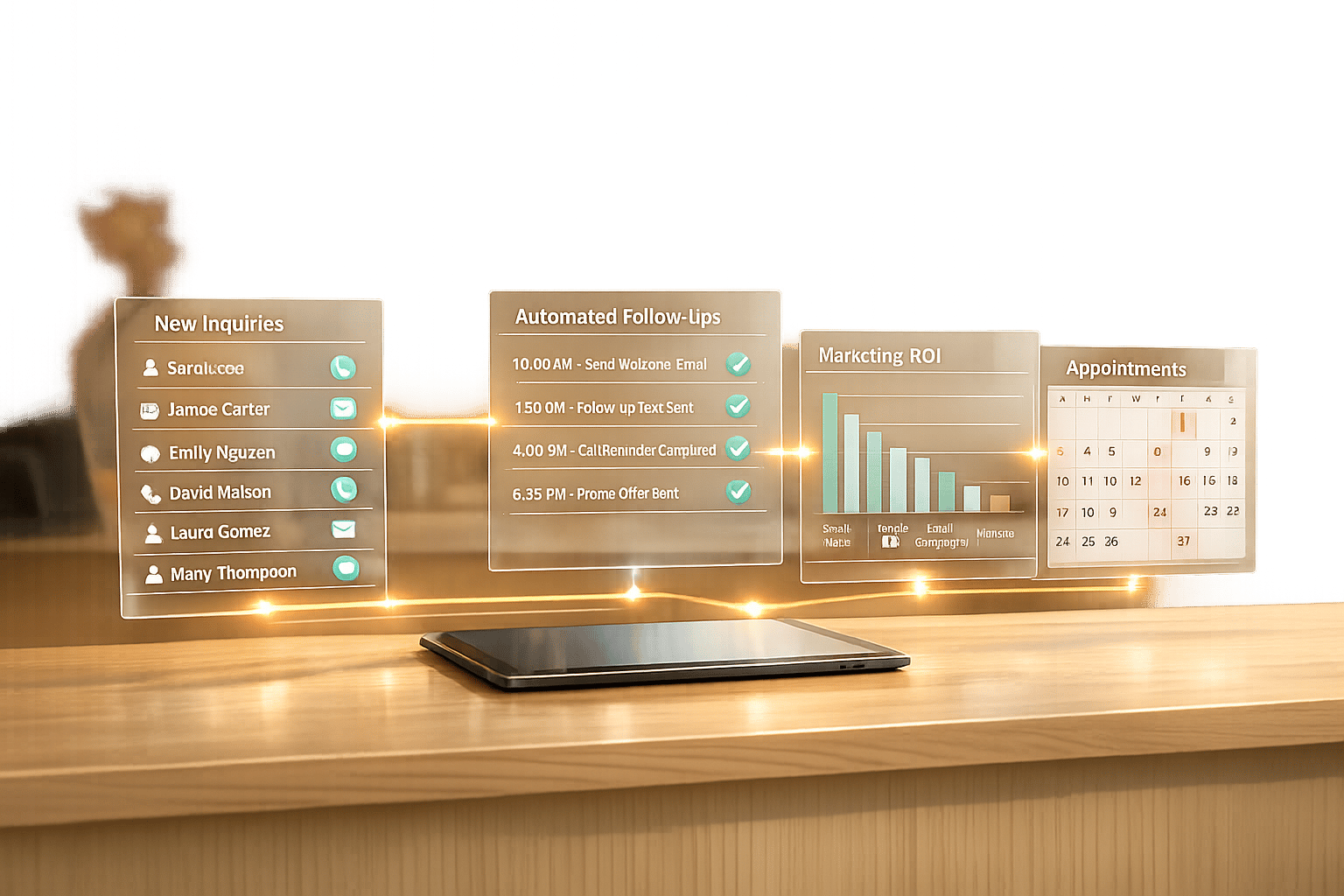
The right practice management software is key to maintaining HIPAA compliance. Many clinics rely on separate systems for scheduling, charting, and marketing, which can lead to data silos and increase the risk of breaches. Consolidating these functions into one HIPAA-compliant platform minimizes vulnerabilities and ensures consistent management of patient records across all touchpoints. Platforms like Prospyr demonstrate how integrated solutions can simplify operations while bolstering compliance.
Prospyr's HIPAA-Compliant Features
Prospyr is tailored for aesthetics and wellness clinics, offering an all-in-one solution that integrates CRM/EMR, scheduling, digital intake forms, payment processing, and secure communication tools. Its cloud-based infrastructure encrypts patient data and enforces strict access controls, addressing key technical safeguards such as role-based access and encryption. Digital intake forms protect patient information from the start, and the integrated EMR ensures seamless data flow through charting and follow-up care. The platform also supports HIPAA-compliant email and SMS, telehealth services, eRX, lab ordering, and a secure media archive for patient-related documents.
In 2024, Dr. Daniel Lee, founder of New Life Cosmetic Surgery, transitioned from using multiple systems to Prospyr. This shift resulted in a 50% revenue increase and a 40% rise in booked appointments by streamlining operations and centralizing patient data. Dr. Lee shared:
"We've seen a 50% increase in revenue and a 40% increase in appointments booked since switching away from using several different point solutions to running our practice on Prospyr."
Similarly, SOM Aesthetics, led by CEO Dr. Saami Khalifian, used Prospyr to launch their practice ahead of schedule, hitting their sales targets 21 times faster than expected. Within two days, they generated $40,000 in revenue and surpassed $100,000 in monthly revenue within two months.
Prospyr Plan Comparison Table
Prospyr offers flexible plans designed to meet HIPAA requirements while accommodating the growth needs of practices of all sizes.
| Plan | Key HIPAA-Supporting Features | Best For |
|---|---|---|
| Basic | CRM/EMR integration, smart scheduling, digital intake forms, secure payment processing, HIPAA-compliant email & SMS | Small practices needing essential tools for secure patient management |
| Professional | All Basic features plus lead capture, marketing automation, practice analytics, social media management | Growing practices needing advanced marketing and operational tools |
| Enterprise | All Professional features plus membership management with automated renewals, task management, review management | Large practices requiring comprehensive tools for patient engagement and staff accountability |
All plans are built on Prospyr's secure, cloud-based infrastructure, providing the essential features needed for HIPAA-compliant patient record management. The right plan depends on your clinic's size and whether you require advanced tools like marketing automation, membership management, or detailed analytics to monitor compliance and drive performance.
Conclusion
HIPAA compliance is a continuous effort to protect patient information and maintain trust. The checklist provided offers a strong starting point: appointing Privacy and Security Officers, conducting regular risk assessments, implementing safeguards across administrative, physical, and technical areas, signing Business Associate Agreements, training staff, keeping audit logs, and preparing a breach response plan. These steps are essential for addressing the rising threat of data breaches and safeguarding sensitive patient data.
The cost of non-compliance is steep. In 2025, the Office for Civil Rights (OCR) issued fines exceeding $8 million, with Tier 4 violations carrying minimum penalties of $68,928 per infraction. For example, the University of Rochester Medical Center faced a $3 million fine for failing to encrypt high-risk devices, and Anthem paid $16 million after weak authentication controls exposed 79 million records. These cases highlight how compliance failures can lead to substantial financial losses and damage to reputation.
Technical safeguards play a critical role in balancing compliance and operational efficiency. A HIPAA-compliant practice management platform can help eliminate data silos and security vulnerabilities that often result from using multiple systems. When functions like scheduling, charting, communication, and payment processing are integrated into a single encrypted, access-controlled environment, both security and workflow efficiency improve. As Dr. Danielle Kelvas emphasizes:
"When you commit to safeguarding your patients' data, you're playing an essential role in the collective trust of the healthcare industry. And there's no goal nobler than that!"
Integrated platforms also simplify compliance for practices. For example, Prospyr offers solutions tailored for aesthetics and wellness clinics, combining patient management, communication, digital intake, and EMR functions. With built-in encryption, role-based access controls, and secure data handling, Prospyr addresses HIPAA's technical requirements while optimizing daily operations and enhancing patient care.
Ultimately, protecting patient data demands vigilance and a technology-driven approach. By following these steps and adopting compliant technology, your practice can meet HIPAA standards, avoid costly penalties, and uphold the trust that is vital to long-term success.
FAQs
What’s the fastest way to fix the biggest HIPAA risks?
To tackle major HIPAA risks efficiently, prioritize security measures and compliance protocols. Begin with a thorough security risk assessment to pinpoint any weak spots. Train your staff on HIPAA guidelines and introduce clear, enforceable policies. Protect electronic records using encryption, strict access controls, and consistent audits. Streamlining tasks like policy updates and staff training through automation can help simplify compliance and minimize risks.
Which vendors need a BAA in my practice?
Vendors that deal with Protected Health Information (PHI) on your behalf are required to have a Business Associate Agreement (BAA) in place. This applies to any vendor involved in processing, storing, transmitting, or maintaining PHI. The purpose of a BAA is to ensure these vendors adhere to HIPAA regulations, safeguarding sensitive patient information.
How do I handle a patient record request without violating HIPAA?
To manage patient record requests while staying compliant with HIPAA, focus on a few key practices:
- Respond promptly: Federal guidelines require responses within 30 days, but check state laws as they may demand faster action.
- Ensure secure delivery: Provide records through secure methods to protect patient privacy.
- Limit shared information: Share only the minimum necessary details unless the request specifies otherwise.
- Verify third-party requests: Confirm the legal authority of any third party requesting access to records.
- Consult legal experts: When in doubt about a specific request, seek advice from legal counsel.
Keep in mind there are exceptions to disclosure, such as cases where releasing records could harm the patient or when dealing with sensitive information like mental health documentation.